AI's data gravity to consolidate cybersecurity, CrowdStrike as a winner
CrowdStrike vs Palo Alto Networks
CrowdStrike is the clear leader in endpoint security, both in the cloud and in its bread-and-butter end devices business. The cloud exposure is a particularly interesting one, as with the rise of microservices and containerization, there has been an explosion of endpoints in the cloud which have to be protected. This is a topic which we’ll go into in a bit.
Corporations adopt endpoint security to secure all their end devices coming into contact with the internet. These include desktops, notebooks and smartphones, and it basically entails making sure that no malware gets installed, monitoring the devices with behavioral analysis to detect suspicious activity, encryption of sensitive data, and making sure no blacklisted apps or websites get visited. The way this is done is by installing an agent on the end device which also sends data to a central monitoring system.
The endpoint is an interesting field in cybersecurity as this is where by far most of the data gets collected as well as where most of the breaches occur, i.e. a hacker gaining entry. Due to AI, responses to security incidents can increasingly be automated, and this is particularly good as there is a large shortage in cybersecurity engineers. We know that the competitive advantage in AI is gained by access to data, i.e. both quality and quantity of data. And data gravity is the idea that large amounts of data tend to attract other data, applications, and services towards them. So one of the theses which we’ll be exploring here is to what extent Crowdstrike should be able to leverage its strong position in endpoint security and turn that advantage to consolidate in the space.
Cybersecurity is a space within software which remains ripe for consolidation. In each particular field, which usually gets designated with its own and unique acronym, we can easily often see still 10 to 20 players handling workloads. However, as the field moves from purely manual responses to automated ones driven by AI, the best players with the data and AI know-how can provide a compelling solution to make the switch away from legacy systems. This is especially attractive as cybersecurity remains a high-growth area, one where CIOs are planning to increase most of their spending. So on top of this attractive industry growth, the best companies should be able to compound revenues at higher rates driven by additional market share gains.
Taking a hugely oversimplified view of cybersecurity, the endpoint is CrowdStrike’s original business, and the company has subsequently been moving into adjacent fields such as cloud, incident response, Security Operation Center (SOC), and identity by leveraging their core technology. So CrowdStrike is becoming a diversified player in the industry with plenty of data access.
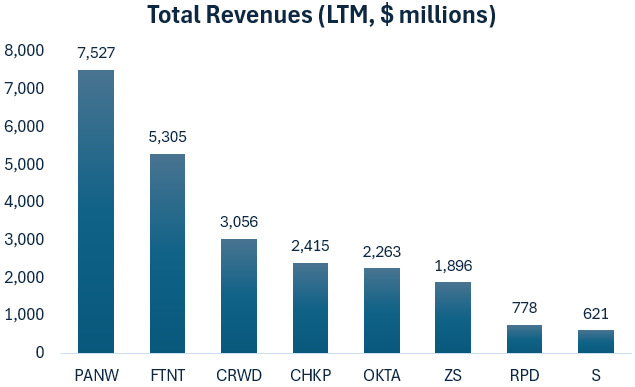
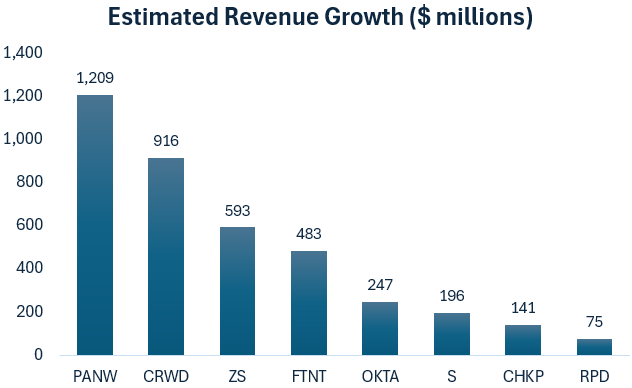
Looking at revenues of the listed players, CrowdStrike is one of the largest companies in the field:
While Palo Alto remains the gorilla in the field thanks to its next-gen firewall business, CrowdStrike is due to its higher growth rate adding almost as much revenues this year as the gorilla:
This is CrowdStrike’s CEO George Kurtz commenting on where there platform fits in into the landscape:
“So when I started CrowdStrike, it was really to have a single platform, a single agent and a single interface that has the best-of-breed technologies in one platform. That's really what I call best-of-platform today and this is what customers are looking for. We don't do everything in the security space, we do a nice piece of it, but customers look at what we have and connect to a Zscaler or connect to someone else (for networking security). They want to be able to take the best of platforms and plug them together as opposed to be saddled with point products kind of masquerading as a platform.
5 to 10 years ago, endpoint was a McAfee or Symantec anti-virus product, that is not endpoint today. There's a module sure that does prevention, but once the data is collected, it's collected once and reused many times. And this is a much different model than anything that had been done before, we're solving data ingest and correlation, threat intelligence, file integrity monitoring, identity.. The chassis is an agent, a data set, a data store and a cloud architecture with modules. There's so many outcomes you can get aside from 10 years ago.”
Kurtz giving more details on the platform’s architecture:
“So when you actually get to deploy the product, there's a reason why it's so friction-free. Large cloud customers can deploy 25,000 agents in an hour because it just installs, there's no reboot and we're the only technology that doesn't have a reboot. I learned this lesson when I was at McAfee. We bought stuff where we would have to go into a company and say hey, we got a new agent, it's not integrated and you have to reboot 300,000 endpoints. No one wants to do that. So the fact that we've thought about the small details of getting a lightweight agent of less than 100 MB in, being able to manage it at scale — which is really hard for companies to do — and we only have one release of the agent, we don't make special agents for you or for another customer, that allows that manageability to run the platform very efficiently. This gives us the ability to collect data at scale and that then unlocks all of the other modules. And that is what gives you the leverage in the gross margin. Almost every other module we add is pure gross margin.”
It’s clear that a lot of clever software engineering has gone into this product. And while that isn’t necessarily a moat — as there are a lot of gifted coders around the world — the amount of data that CrowdStrike is collecting and then run a trained AI response model on top of that could form an effective moat. And one that would make it compelling to buy and stick with the product.
There aren’t that many players which could replicate such a system, potentially a Palo Alto or a Microsoft, but CrowdStrike is already head-and-shoulders above everyone else in endpoint and will have the best scale of data going forward, which should bring in the data advantages.
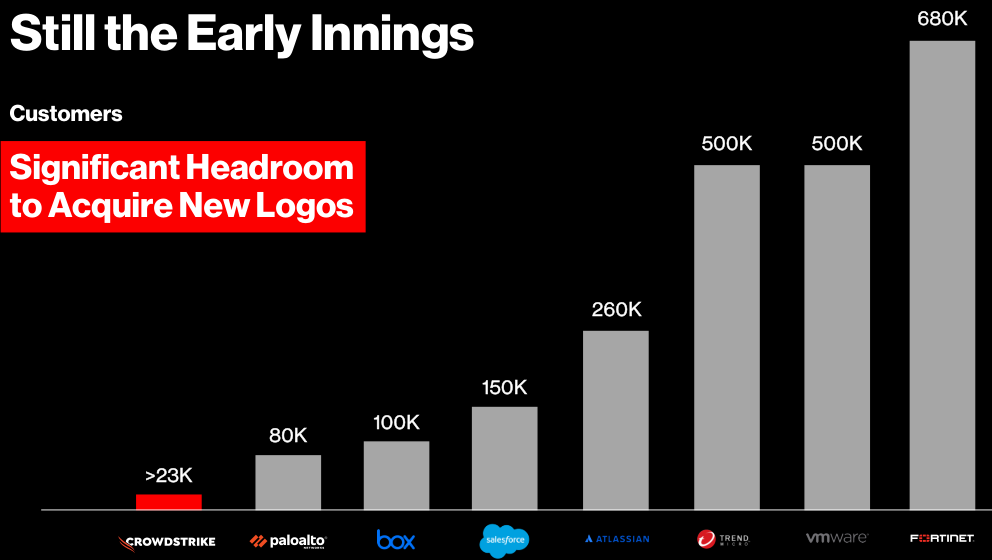
The company disclosed that they have penetrated 30% of logos within the Global 2000 in endpoint, highlighting their strong position already, with still massive opportunities in both the public sector and small businesses with penetration rates of less than 1%. Looking at the number of customers of other software companies, there is plenty of runway for growth:
The other point Kurtz raised about selling additional modules to their customer base is one of the attractions of software platforms in general. The client is already up and running on your software so any additional revenues you make from launching new features are very high gross margin.
To sum up, there are plenty of attractive growth angles in this name. Let’s go through a number of them in more detail, starting with the cloud and microservices.
The explosion in microservices
Modern software architectures have moved from monolithic code bases to isolated microservices running inside of containers. A container is a lightweight virtual environment running inside of a virtual machine or server. Let’s say you have two apps running on one server, one written in Python 3.10 and the other is still on Python 3.8, this could easily be achieved with two containers, as you can install the respective Python version inside each. By contrast, you can’t install both Python 3.8 and 3.10 on one server or virtual machine, so you would always have to update each app’s codebase as you move to a new Python version. Obviously this creates a lot of unnecessary friction.
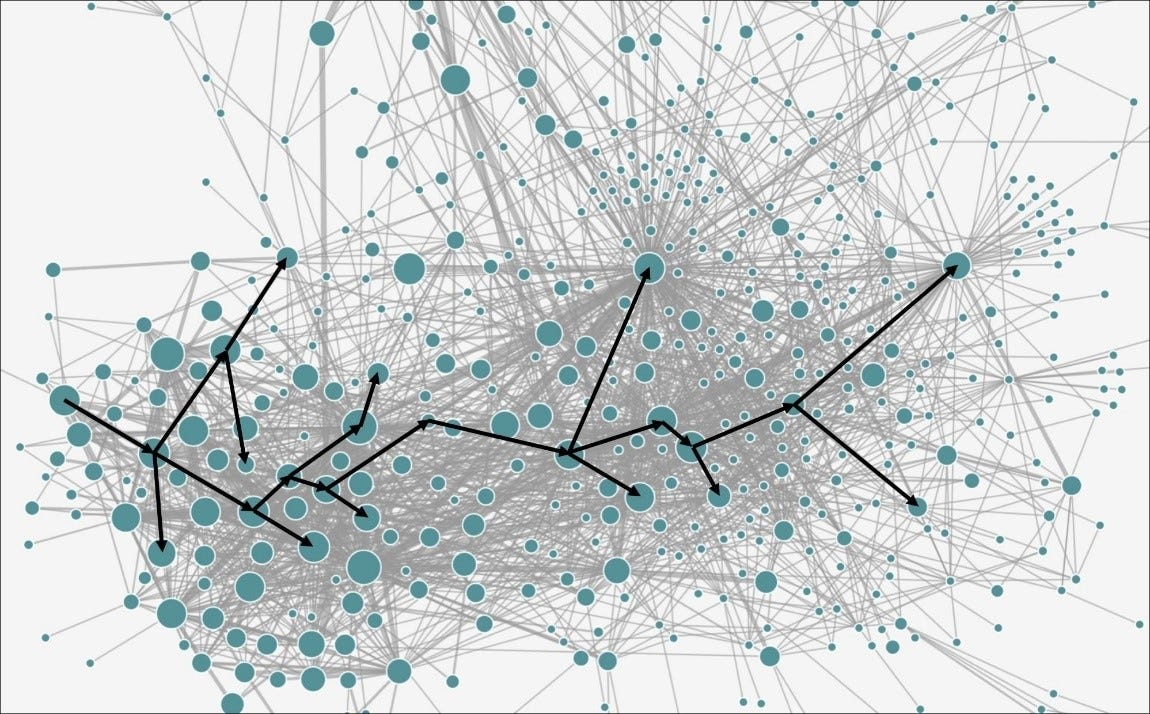
A large company utilizing a microservices architecture such as Netflix can have hundreds or thousands of apps in communication with each other on their servers. Below is an illustration of Uber’s microservices architecture and how a particular request can flow through the system’s needed services. Each bubble on the illustration is a containerized app with its size indicating how frequently it has to handle requests. A fleet of containers like these is managed by an orchestration platform such as Google’s Kubernetes or Docker Swarm, and can be monitored with tools such as Datadog or open-source alternatives like Grafana.
As all apps running in containers expose APIs to exchange information with the outside world, they have to get protected. This is where the field of cloud security comes in, CEO Kurtz discussing the cloud business:
“We started with the hardest part first, which is cloud workload protection. That's really the preventative technology that runs in these virtual environments, in Kubernetes clusters. There's a lot of different ways that you can consume cloud workload protection and that took the better part of 10 years to build, something as robust as what we've built. We are protecting some of the world's largest clouds and largest SaaS platforms. You can't go to a dev team and say, we're going to put a piece of software on there that's going to interrupt what you're doing. So it is really a high barrier to entry to get a cloud agent in a critical workload. Then you combine the piece of cloud workload protection with CSPM (cloud security posture management), application security, and data security posture management, and we believe we've got the best cloud offering in the market. Not only is it best-of-breed in these areas, but the fact that it all works together and can seamlessly identify threats, identify misconfigurations and the big thing, prevent the breach.”
Kurtz discussing the growth in the TAM of this business, driven by virtualization and containerization:
“If you take a physical server and move it to the cloud, it equates to like ten different workloads, just how everything is split out in Kubernetes environments. I think it massively expands the TAM. If you look at where the growth is in protecting workloads and endpoints today, that isn't going down. The proliferation of agent and non-agent technologies, look at things like enterprise attack surface management, these were things that people didn't even consider 5 years ago.
The technology curve, as it gets more complicated, security has to parallel the slope of that technology curve. So if we just think about 30 years ago, you had a simple website and a firewall, really easy. Today, it's incredibly complex when we think about all of the different cloud environments, and that's only going to get more complicated. Ninety percent of the active incident responses that we're working on right now are all cloud-related exposures. So I think we're only in the early innings of what we're seeing in terms of cloud protection.”
CrowdStrike and Palo Alto are the two strong players in this field according to Forrester (below) and as the business grew at a 90%-plus rate over the last year and is now generating over $400 million in revenues, obviously we have a very interesting asset. Morgan Stanley commented that CrowdStrike is the fastest growing player in this area and at the capital markets day, the company mentioned that 28 out of the Fortune 100 are already customers for this product.
An advantage CrowdStrike has here vs Palo Alto is that the latter is running its endpoint and cloud security products from different platforms, whereas with CrowdStrike, everything is integrated into the single Falcon platform. Kurtz on the recent earnings call:
“A global financial services giant replaced their Palo Alto Prisma Cloud products in a large 7-figure deal. The Palo Alto cloud security products required separate management consoles and separate agents because cloud security is on a separate Palo Alto platform altogether. CrowdStrike was able to deliver an expected 70% time reduction in management as well as more than $5 million in annual staffing cost savings. The patchwork of multi-product, multi-agent and multi-console separate platform technologies resulted in visibility gaps, asynchronous alerts and overall fatigue managing cloud security. Falcon's single platform with its integrated cloud security component was a win for the customer.”
AI data advantages to consolidate cybersecurity
Cybersecurity has been a very fragmented field with still many point solutions lingering around. Large vendors such as Palo Alto and CrowdStrike have been talking up how they’re building automated AI response and detection systems trained on the large amounts of data they’re collecting. This is Kurtz on this topic:
“We have one of the biggest datasets around. But it isn't really about the size, it’s about annotated data, how you collected it. Over the last 10 years through OverWatch, which is our managed detection and response service, we've been able to annotate a lot of these threats, i.e. pairing this data. So now when we train the algorithms, we not only have the threat data, but we have: is it real, is it not real, et cetera. So when this goes into the algorithm, it comes out with better efficacy on the other side. And that took 10 years to build up, so we look at that as a data moat.”
CrowdStrike has one of the largest breach response businesses in the world, together with Google’s Mandiant, so this is another interesting area where they can collect annotated data from. Kurtz discussing this business:
“The two biggest companies that do this are us and Mandiant, and both are the key quality players that are responding to these breaches. So this really gives us a leg up. Not only do we see all this activity from our cloud, but you're really at the tip of the breach and it allows us to always understand what's happening in the environment. So we are trusted advisers for organizations. When you deploy our technology in an incident response, it's up and running. You can't do a twelve week deployment in an incident response, you got to get it up and running that day and this is what we do. And we actually work with many of the service providers, Mandiant will use our technology as part of an incident response. That's the way we see this as a force multiplier.”
And this is Palo Alto’s CEO, Nikesh Arora, on how AI can drive consolidation in the industry:
“Most enterprises have about 30 to 40 security vendors. They collect data from these and then try and cross-correlate it. It doesn't work like that, you need a single source of truth. So what we did internally is we took our business, where we had 67,000 alerts across 200 vendors and we've replaced all of that with one endpoint from ourselves. We took our mean time to respond from 27 days to under one minute by using AI and that's the product we put in the market called XSIAM. That concept will be the disruptive event in security in the next 5 years. If there’s a ransomware attack, from the point in time they attack a company until the time they've extracted petabytes of data, this can be 14 hours. So you have to be able to stop the threat in less than 14 hours. Today, the mean time to respond for most companies is measured in days, which means everybody is susceptible. And another big problem is that there's a massive shortage of labor in cybersecurity, I've read that the industry is over 3 million workers short.”
So these drivers should bring in a long awaited consolidation phase in the still overly fragmented cybersecurity landscape. There is lots of scope for consolidation, Kurtz explains:
“If you're a point product or you don't have as much value, that's going to wane over time. Some customers have 60 different security vendors. Interesting story, I was talking to a CISO a number of months back where they called me on a Friday at 5 and said hey, we've got this issue and we want to have your response guys come in, we found something. They had 60 different security products, 60 different controls, and we were the only product and technology that caught what was happening, it was actually a Mandiant pentest. They have too much stuff and they're actually looking at the controls, what's working, what isn't working, and want to consolidate on CrowdStrike across the stack.”
Kurtz also mentioned that 50% of companies are still on legacy antivirus products, although I suspect this will mostly be in the SMB market. So additionally there is still quite some runway for modern endpoint protection systems to grow, especially as a ransomware attack can be fatal for a business. And CrowdStrike has also introduced a simplified control panel for the SMB market, something that can easily be managed by one person.
This is Palo Alto’s CEO on the endpoint market:
“We were not a player in endpoint five years ago when I joined. There are 14 endpoint companies, there was Symantec, McAfee, Carbon Black, Cybereason, Cylance, CrowdStrike, a whole bunch of others. Now it is down to CrowdStrike, Palo Alto, Microsoft and SentinelOne, the other 10 are over time going to get replaced. And to the extent somebody already has just recently deployed one of the other three, we will ingest data and make it work on XSIAM (Palo Alto’s AI-driven Security Operations Center), we will take that friction out of the system.”
CrowdStrike is now also building up a generative AI, Charlotte, to take over security workloads and this sounds very promising. Kurtz explaining this new product:
“Let's look at what a Tier 1 analyst does today. In their 8-hour day, he basically logs in, goes through alert triage, tries to figure out what’s the priority, and then takes action and writes a report. There's a lot of work that goes into it, people click around and triage. Where we see this going is to create what we call generative workflows, which is Charlotte. So in the morning you would come in and Charlotte would say what the latest threats are that CrowdStrike knows about, how does that apply to the assets in your company and mitigating actions to take. Maybe you want to roll out a patch, create a PowerShell script on the fly and then use FalconFusion, which is our automated workflow. So our whole goal is to take 8 hours of really mundane work and turn this into 10 minutes. We have a whole workflow built in, every service on the platform can use it, and that's where the value comes in. You can't find enough security people, they're too expensive and hard to keep. The real value is in automation and taking the cumulative knowledge of CrowdStrike and all of our threat hunters.
When we think about pricing, it comes down to value pricing, what would it cost for a team of analysts? And for us, we want to strike a balance of making sure that customers use it versus overpricing. We've seen other pricing from competitors out there that I think is just way overpriced. The focus is to get everyone using it because when you actually see it, it's sort of like one of those iPhone moments, people are going to be really hooked and use it in ways that we hadn't even thought about.”
CrowdStrike expands the Falcon
As already touched upon above, the company has been busy building out new modules which are integrated into their Falcon platform. One is identity, Kurtz going into this module:
“Identity is a broad category and we break it into 3 areas, you have identity creators such as Microsoft, then you have identity aggregators, which would be a Ping and an Okta, and then you've got identity protectors like CrowdStrike, the ability to actually prevent the identity from being abused and to prevent lateral movement. We acquired a really great company and what we did, we took their technology, with a great team, and we carefully rewrote it into our agent. Our brand promise to our customers is a single agent architecture. Once we did that, we went mainstream with the sales force and then all of a sudden, it was one of the fastest-growing modules in the history of CrowdStrike. Because all you need to do is turn it on. If you're just using EDR without an identity product, that would be a gap, and we're the only technology in the marketplace that’s single agent with identity protection built in. Other players have multiple agents, or not even the same capability in their core protection product.”
SIEM is the field in cybersecurity where all the logs are being analyzed to find potential breaches and penetration attempts. This is quite a crowded field with Splunk, Microsoft and Elastic being the strong players. CrowdStrike is now going into area as well with they call ‘next-gen SIEM’. Kurtz discussing the market:
“SIEM is a hodgepodge of technologies that are generating alerts and information by correlating data together. Over the years, we've had customers look at our technology and say do I even need a SIEM? I've had customers take their SIEM budget and just buy a CrowdStrike. Their end goal wasn't log management, it was to find and stop breaches, and we’re able to do that. When you look at the SIEM market today, you have a lot of customers that spend a lot of money. It's very expensive for data ingest and they're still piecing all this information together. A key part of our technology is that we never lose the context from the endpoint or the workload, we have a huge graph in the cloud. What happens in the SIEM world, you have a lot of companies that ship log information to a SIEM and you lose all the context. With CrowdStrike, we have about 85% of the core data that goes into a SIEM and with LogScale, it is natively built in into our platform. We think we're really in pole position because the critical data is the endpoint data, that's the high fidelity data and what we call next-gen SIEM.
If we think about network data and identity data, those are small amounts of data. Even on the network side, you're looking at network flows, it's very difficult to get deep into the inspection of all this because many of the conversations are encrypted. What customers are looking for is they want to see what actually happened. And that's really where we can instrument to an incredible degree of detail and accuracy. One very large worldwide bank came to us, they were spending a lot of money on a legacy SIEM product and we essentially became their data lake. It's like 40 petabytes of data per day. They didn't migrate off their legacy SIEM but we were able to cut their bill to one-third of what they were paying.
Now with our technology, searches that were taking two days take less than a minute. One of the things about LogScale is it doesn't require an index. So what that means, and this is really important in the security world, as soon as you start to ingest data, you get results and you could begin to query it. And in security, time is of the essence. If you have a forensic investigation and you have to wait a day to actually create an index, you just lost a day.”
This business was basically built up by the Humio acquisition, a log management and observability platform which CrowdStrike then integrated into its Falcon platform. Take what he said about their index-free searches being unique with a grain of salt, open-source observability platform Grafana has similar capabilities for example.
CrowdStrike flagged some interesting wins in next-gen SIEM on their recent call:
“One of many noteworthy wins from the quarter was in partnership with Deloitte, which has a hyper-growth LogScale next-gen SIEM practice. Together, we closed a 7-figure multi-year next-gen SIEM deal with a large European manufacturer displacing Splunk and Elastic and beating out Azure's Sentinel. This customer now has 16 Falcon platform modules deployed.
A major mobile computing company standardized on LogScale next-gen SIEM in a 7-figure multiyear deal replacing legacy SIEM. We competed against Palo Alto's XSIAM. The customer was looking for an open architecture versus a closed vendor locked-in approach to cybersecurity. The complexity of having to deploy many different Palo Alto products and multiple agents made CrowdStrike an even easier choice.”
To reduce delays between security and IT teams working together to solve issues, CrowdStrike has now also made Falcon accessible to IT personnel. Kurtz on this new module:
“Particularly through the pandemic, customers were using CrowdStrike to patch their systems. We have an airline as customer and when they have an issue with their kiosk, they actually use CrowdStrike to remediate that, just on the IT side. And the list goes on. So if you can script it, you can automate it, and we've got full automation already built in into the product. Many of these teams have come to us and said every time we find an issue, we have to put it into a ticketing system and it then gets shipped over to the IT group. So what we decided was we wanted to give the IT folks a place where they can actually do work. Today, it is the number one requested module we have.”
The company is now also expanding into data protection, Kurtz discussing this at the recent Morgan Stanley conference:
“So when we looked at the DLP (data loss prevention) market, it really is analogous to the legacy AV (antivirus) market. You have high dissatisfaction rates by customers, you have a product that doesn't do all that much, it checks a box for compliance, and it's expensive to manage. Most of the large banks, they probably have 50 people in their DLP group, just doing rules and things of that nature. So we spent the last two years working with our customers. We acquired a company called SecureCircle, we just needed a few bits of that, and then we came out with Falcon for Data Protection. We just launched it last week and we already have paying customers because they were helping us.
In today's world versus 10 years ago, data is not just generated on your laptop or on a server, but now it goes out to a SaaS application or to a cloud infrastructure provider, and it's really about the flow of data. So that’s why we did the Flow acquisition. We now have the ability to understand the flow of data, we can track it back to identity, who owns the data or who touched the data, and then you can track it back into the hygiene of the system. That's what Flow does. Not only does it understand the data flow, but it can actually prevent leakage. So we think that is going to be best-in-class in the industry.”
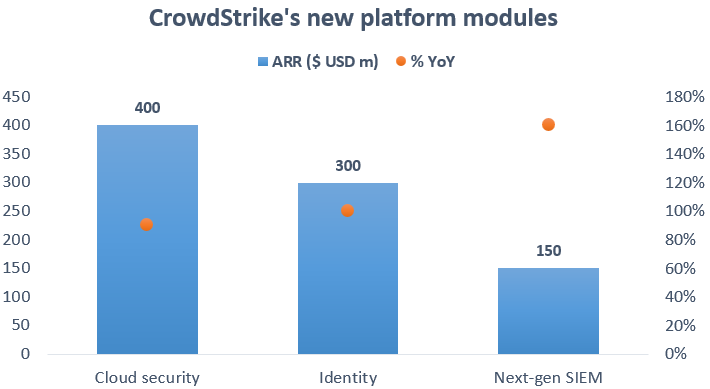
Clearly these new modules are doing well, generating already over $850 million in annual recurring revenues (ARR) and growing at a rate of over 100% year-on-year:
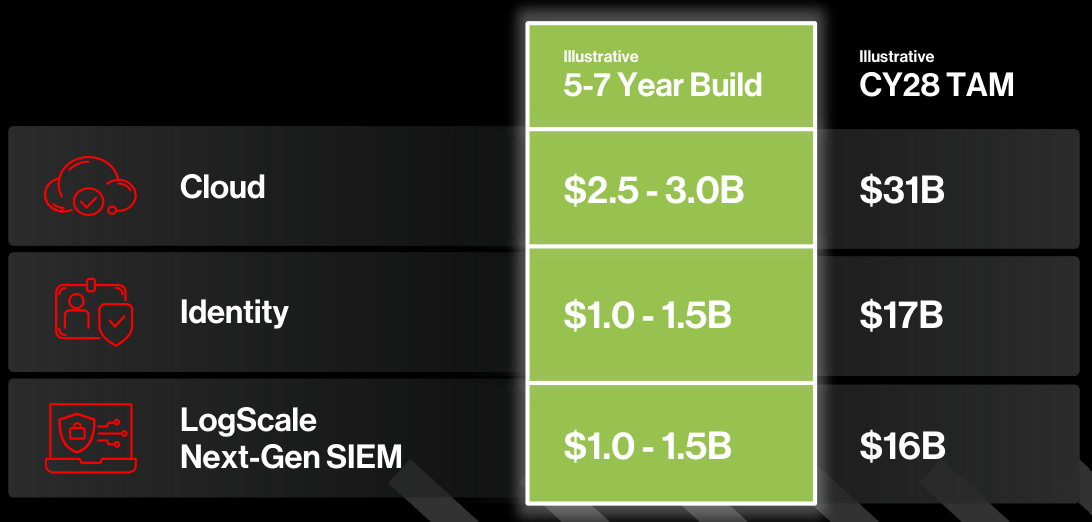
And long term these TAMs are large. If the company builds their cloud security module into a $3bn revenue business, this would still only translate into a market share of around 10% in ‘28:
Palo Alto declares war
Basically what Palo Alto Networks announced on their recent conference call is that they will allow clients to delay payments while they get up and running on the company’s platforms. The main aim is to make it easier and more budget friendly for customers to transition to Palo Alto’s bundle while they have to run their legacy products side by side during the transition period. I do think this is smart strategy and while this will weigh on revenue growth in the near term, the revenue uplift should come in the medium term as it will allow more customers to harmonize solutions. This is Palo Alto’s CEO on their strategy on the recent call:
“We're beginning to see rogue behavior by some vendors in the space who are keen to retain their customers, primarily in the legacy and startup spaces. We intend to combat that with investing and trying to accelerate platformization and consolidation for our customers. We're also seeing increased demand for deploying AI in our products. Putting this all together, these trends of the market bolster our conviction that adopting platforms is the only viable strategy for customers. Customers have adopted platforms in other markets across technology, and this will inevitably happen in cybersecurity. Until now, we have primarily assumed that our customers adopt our platforms at their own pace. The crux of challenge is around execution. Customers face risk in executing, or making significant changes to their environments, as well as in economic exposure from these changes. Key friction points we've noticed include the challenge of replacing multiple products simultaneously as well as the issues around double paying while working through complex contract terms. Over the last 6 months, we have been quietly working to develop programs that enable us to help minimize and even share in the risk of our customer space. You will see us tomorrow launching a significant number of platform offers to help drive this consolidation. We believe we can build customer confidence in our platforms by approaching them well before their point product contracts expire. After we gain their contractual commitment, we have offered an extended rollout period where we can demonstrate our ability to deliver these platform benefits. Customers can then start paying us after the obligations to legacy vendors ends.”
This is Kurtz on the topic at Morgan Stanley:
“Platformization is a new term for discounting, bundling, and giving products away for free. This is not anything new and happens in security all the time. Look at their endpoint product, they bought the thing in 2014 and they've been given it away since then. It's got like a single-digit market share. So from our perspective, I don't think it's anything new. Ultimately, I think the best platform wins and we think it's going to be us.”
Palo Alto is the big player in the overall space and the one who has been most assertive in trying to consolidate it by building out a set of platforms addressing various end-markets, from next-gen firewalls to SASE and EDR, making them a competitor to a wide variety of players. So Palo Alto being bashed by one of their competitors is nothing new and this happens quite frequently in the industry. I do think Kurtz is right here that Palo Alto will struggle against them in endpoint security, and thanks to CrowdStrike’s single platform, that the latter is the stronger player in cloud security as well. However, I do expect Palo Alto to get a good share as well, and a bundle comprising also next-gen firewalls and network security should be attractive for a lot of companies.
SEC regulation as another tailwind for the space
Cyber and ransomware attacks have been on the rise and the consequences can be extremely dire. One of the worst examples was when Colonial’s pipeline system was halted for a stretch of five days during 2021:
Regulation is now being stepped up for companies to protect their infrastructure better. Going forward, listed companies will have to disclose within 4 days when they’ve become aware of a breach. In addition, companies are also required to provide updates on previously reported incidents and to include information about their cybersecurity risk management, strategy and governance in their 10Qs and 10Ks. This should lead to a higher demand for better cybersecurity systems, both to prevent breaches but also to get a more detailed and rapid assessment of the extent of a successful attack.
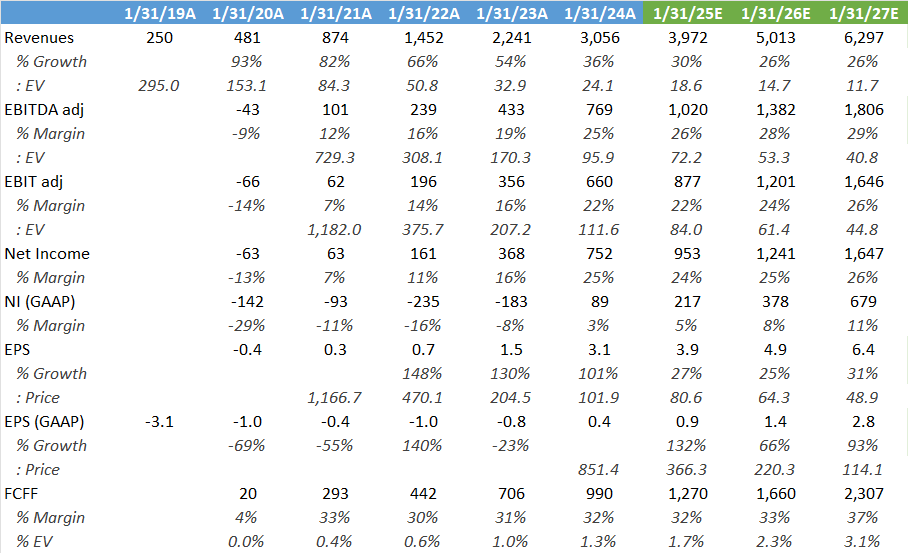
Financials — share price of $315 at time of writing, ticker CRWD on the Nasdaq
Wall Street’s estimates below which look reasonable, I think there is probably a bit more upside on the margin. While the company spent 0.8% of the market cap on SBC over the last year, FCF generation is extremely strong and can start being redirected to offset this dilution via buybacks. Overall the company has a bit less than $3 billion in net cash on the balance sheet. Valuation is pretty demanding at 81x 2025 adjusted EPS and obviously the company will have to keep executing extremely well, but you do get a company which can become one of the big winners in cybersecurity and which is still generating 30%-plus top line growth coupled with margin expansion. The FCF yield is starting to look attractive, at 1.7% expected for this year.
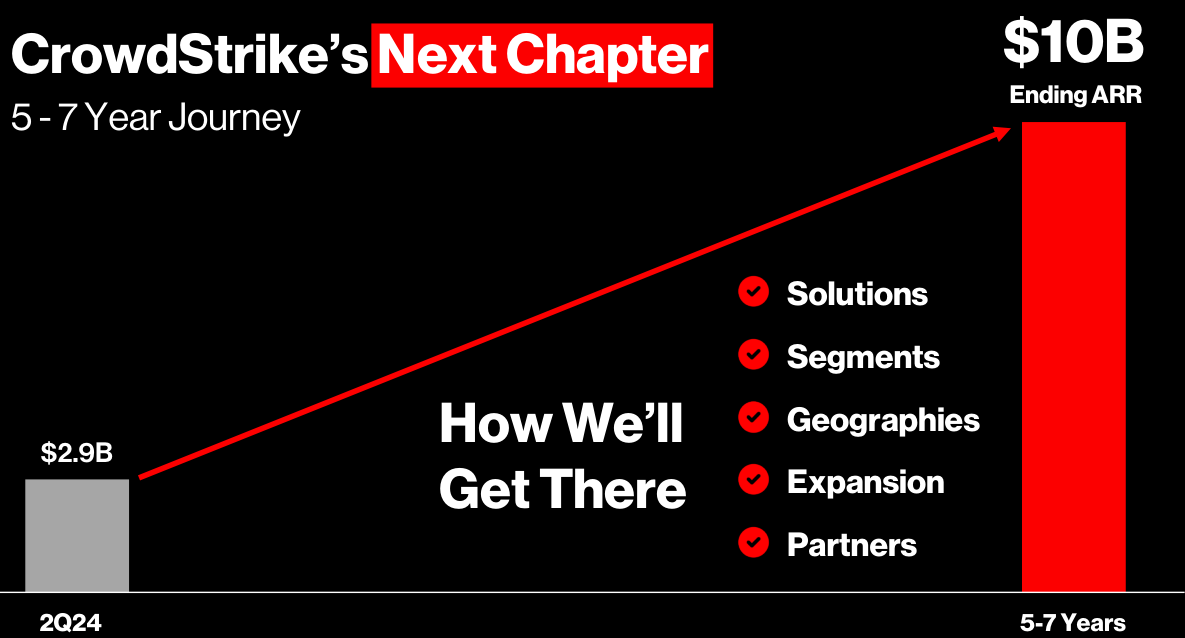
Close to 70% of revenues are still being generated from US headquartered companies, so there is long path for growth in the rest of the world. Overall, the company is targeting over $10 billion in annual revenues within the next 5 to 7 years:
This seems doable as the company is one of the strongest players in a massive $100 billion market today and which is expected to grow to $225 billion by 2028. So $10 billion in revenues would give them a market share of less than 5% in five years’ time.
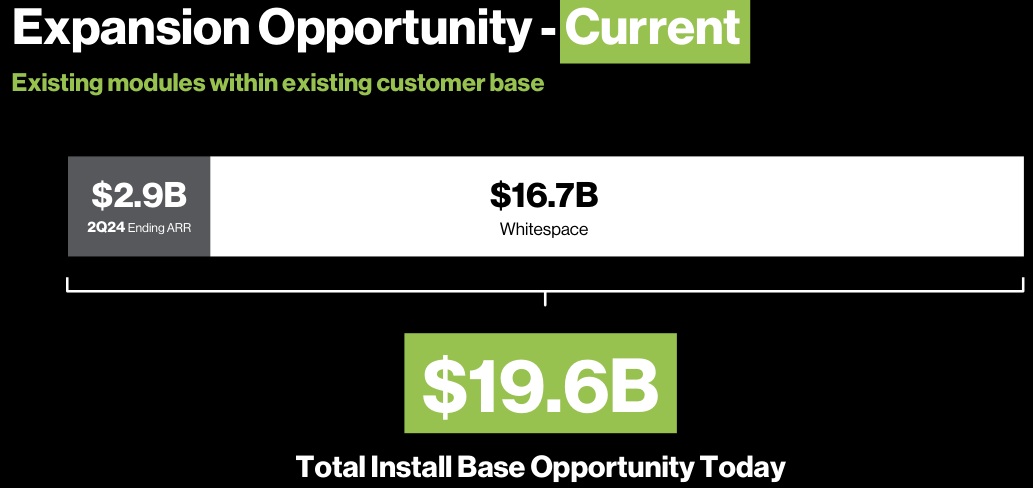
As a theoretical exercise, if the company could transition their customers to use of all their modules, this would give $20 billion in annual revenues:
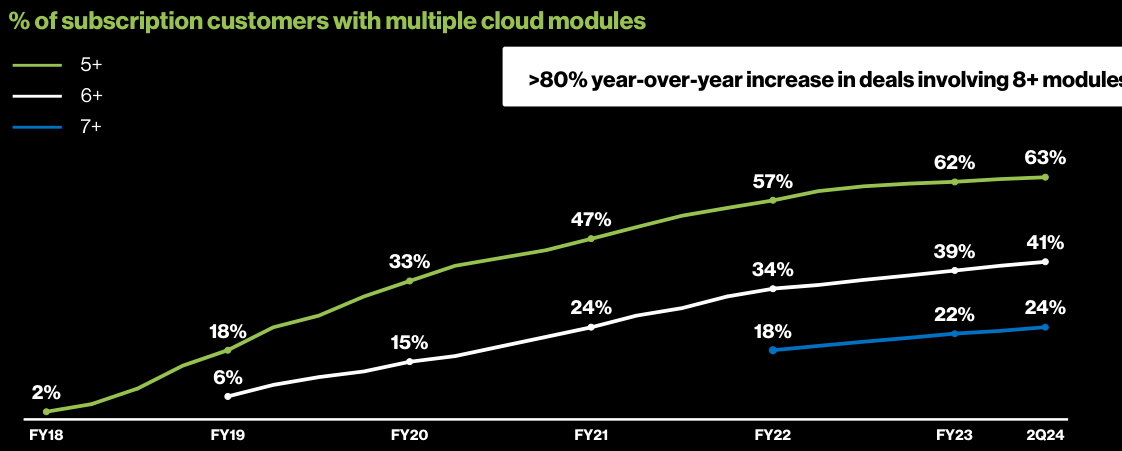
Over time clients do sign up for more modules, the company illustrated how the number of customers taking more than 5, 6 and 7 cloud modules has been on the rise:
Management expect EBIT margins to rise to 30% within 3 to 5 years which certainly seems doable:
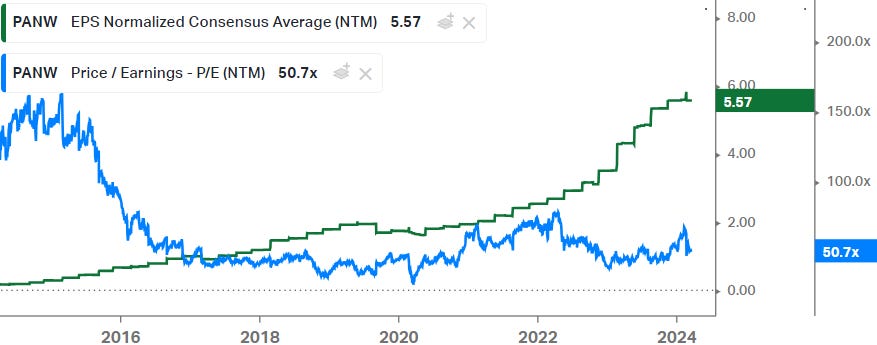
For comparison, below is Palo Alto’s EPS progression and forward PE trading history:
Overall, I still like CrowdStrike here. Together with some of the other quality players in the cybersecurity space, I do expect them to be among the long term winners. And they do look to have a competitive advantage versus Palo Alto which has been stitching solutions together into three platforms really, CrowdStrike on the contrary is running everything from the single Falcon platform.
Cloud, consolidation, new modules, AI and growth beyond the core US market, all of these should result in a long runway of EPS growth. Even when growth starts maturing, quality software names can easily still trade on attractive multiples from 20x to 35x forward PE given the stickiness of the business. So whereas the shares have had a good run already, I do think that these still have good compounding potential over the long term.
If you enjoy research like this, hit the like & restack buttons, and subscribe if you haven’t done so yet. Also, please share a link to this post on social media or with others who might be interested, it will help the newsletter to grow, which is a good incentive to publish more.
I’m also regularly discussing tech and investments on my Twitter.
Disclaimer - This article is not a recommendation to buy or sell the mentioned securities, it is purely for informational purposes. While I’ve aimed to use accurate and reliable information in writing this, it can not be guaranteed that all information used is of this nature. Before making any investment, it is recommended to do your own due diligence.









Brilliant article. Thanks very much for all your insights.
I agree, $CRWD has a lot of momentum, and the management execution is excellent!